Types of Malware
Before malware became such a present menace, viruses were considered the biggest threat to computer systems. In fact, many people still falsely consider antivirus software sufficient catchall protection for all types of malware.
While computer viruses are still a major problem, many types of malware have surpassed viruses in variety and threat level. Today’s most malicious software can self-replicate and harm your computer without your knowledge or permission.
Knowing the most common types of malware—those notorious worms, bots, zombies, and spyware villains—will help you understand and avoid these attacks on your computer and your business.
Killer Worms
Computer worms are one of the most destructive types of malware, as they hide in your computer, probing for other computers on your network to infect.
A worm might infect a computer without any action from you, or it might trick you into opening a link from a Web page to infect your computer. And worms can reproduce fast, replicating as many as 250,000 times in a typical eight-hour workday.
A worm’s capabilities and targets depend on the payload it carries. The payload is the part of malware written to execute a specific task (another part of the code is written to enable its replication).
Payloads can be written to delete files on an infected computer, launch a viral attack, disrupt network traffic, and attack email and social networks for various aims. For example, worms are often used to disrupt network services or create denial of service (DoS) attacks against businesses.
Tricky Trojans
Much like the infamous wooden horse that ancient Greeks used to deceptively enter and destroy the city of Troy, today’s Trojan malware appears to be legitimate but can infiltrate and damage a computer. Victims are tricked into downloading and running the bogus software on their computer systems.
Once installed, a Trojan starts attacking its host computer and may strike by displaying annoying pop-up windows, spreading stubborn viruses, stealing personal data or passwords, or deleting programs and files.
Unlike computer viruses and worms, Trojans don’t spread on their own by infecting other files or by self-replication. Instead, they engage unsuspecting users to create computer damage themselves by opening an email attachment or downloading a file from a website offering interesting games, quizzes, or software.
Such seemingly innocent actions can wreak havoc if you allow Trojans to access your computer. Some may even uninstall files, opening up a back door to your security system. In this way, Trojans can allow an outside user remote control of your computer to copy and resend confidential information.
Panda Labs, Panda Security’s anti-malware laboratory, reports that in the first quarter of 2012, six million new malware samples were created, and Trojans now represent 80 percent of all new malware. As you can see in Figure 4.1, no other malware comes close, as even worms comprise just 9 percent of total malware.
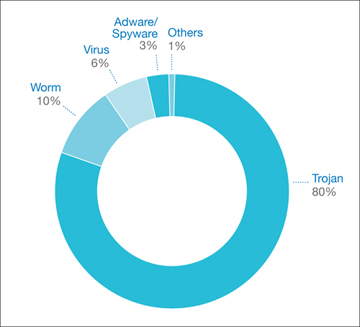
Figure 4.1. Wondering what malware to combat most? Trojans account for 80 percent of all malware attacks.
Source: Pandasecurity.com
Bad, Bad Bots
A “bot,” short for robot, is advanced malware that poses a major threat to almost any computer or mobile device.
Bots give cybercriminals major control over their victims’ computers. Bots use infected computers, known as “zombies,” to send spam, host phishing websites, execute DoS attacks, or steal victims’ identities by monitoring keystrokes.
A collection of bots in a network, or a botnet, can be deployed by organized cybercrime bot-masters to sell bots for malicious and illegal purposes. Bots have contributed in recent years to much corporate spying, government surveillance, and distributed denial of service (DDoS) attacks, which can shut down computer networks by accessing servers repeatedly and preventing legitimate customers from accessing websites.
Security experts say that there are thousands of bots and zombies on the Internet, and many may operate unnoticed for months as unwary computer owners endure their computers slowing down, showing strange messages, or crashing.
Prying Spyware
Fighting viruses, worms, Trojans, bots, and zombies has become a requirement for most businesses, and online security vendors have their protection down to a science.
However, another newer malware is using increasingly clever and sophisticated ways to sneak onto vulnerable computers: spyware.
Spyware is malware that gathers information from your computer without your knowledge and gives it to another party. Some irritating yet fairly harmless types of spyware may steal a computer’s power and memory, causing it to run slowly or even crash.
However, more dangerous spyware can steal your personal and financial data, such as your home address, email address, account passwords, credit card numbers, and more. And online merchants beware: scammers using spyware can get even more critical and useful data (for criminal purposes) about hundreds or thousands of your customers.