- Reference 2.1 Understanding Apple’s Goals
- Reference 2.2 Device Management and Supervision
- Reference 2.3 Apple ID Considerations
- Reference 2.4 iCloud in Managed Environments
- Reference 2.5 Apple Deployment Programs
- Reference 2.6 Deployment Scenarios
- Exercise 2.1 Configure Your Client Mac
- Exercise 2.2 Create Apple IDs
- Exercise 2.3 Verify Administrator Apple ID Access
- Exercise 2.4 Configure Your iOS Device
Reference 2.3 Apple ID Considerations
An Apple ID is how Apple services identify you as an individual. Apple doesn’t care about the PIN you use to lock your iOS device or even the account you use to log in to your OS X computer. From Apple’s point of view, those other identifiers are all secondary to your Apple ID.
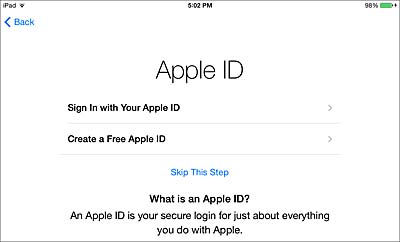
Case in point, when setting up a new iOS or OS X device, the Setup Assistant asks for your Apple ID before any other personal or security settings. In fact, signing in with your Apple ID during Setup Assistant affects all the first-time configuration steps that follow.
Make no mistake, you don’t need to sign in with your Apple ID to set up an iOS or OS X device, but you do need to sign in if you expect to use any of the Apple services that integrate so well with these devices, including the App Store, iCloud, and Apple Deployment Programs.
Unfortunately, many IT administrators are confused about the best methods for organizing the usage of Apple IDs, or worse, try to circumvent proper Apple ID usage as part of their management plans. In this section, you’ll learn the best practices for creating and using Apple IDs in managed environments.
Creating Apple IDs
You can create as many Apple IDs as you need, and in the case of an administrator trying to mange Apple devices, you will need multiple Apple IDs for various administrative tasks. Your users will also need Apple IDs if they intend to access any Apple service, including the App Store.
You can set up a new Apple ID using any verifiable email address that isn’t already tied to an existing Apple ID and isn’t using an email domain owned by Apple, such as @apple.com. Alternatively, you can also set up an Apple ID without an email address by applying for a free email address hosted by icloud.com. Any non-iCloud email address must be verified by opening a web link embedded in an automated email sent to the specified email address.
Additional information required to create an Apple ID includes entering a secure password, a birth date, a mailing address, and the setup of three security questions and answers. The security questions are used to verify the user during password changes or if the user loses his Apple ID sign in.
The most common methods for initiating the creation of a new Apple ID are:
- When signing in to an Apple website—To access certain Apple websites, you need an Apple ID. Examples include the Apple Support site and Developer site. For the creation of a new Apple ID, these pages link to the website https://appleid.apple.com. You can also manually navigate to this website at any time to create new Apple IDs or manage existing Apple IDs.
- When signing in to iCloud on an Apple device—On an iOS or OS X device, you can create a new Apple ID when signing in using the Setup Assistant or the iCloud account settings. Signing in to iCloud on an Apple device is the only way to enable iCloud services for an Apple ID. It is also the only way to request an email address using the icloud.com domain.
- When signing in to an Apple store—To facilitate purchases, you must associate billing information with your Apple ID. When creating a new Apple ID within an Apple store, such as the App Store or iTunes Store, you will also be required to select a billing address and payment method. When acquiring a free item, you are allowed to select None as the billing method, but you must still select a billing address associated with your Apple ID.
Managing Apple IDs
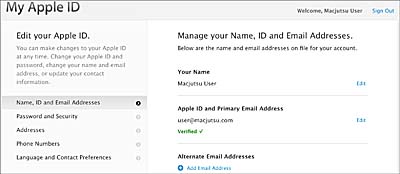
Once created, Apple IDs can be modified by signing in at https://applied.apple.com. There you can change most aspects of an Apple ID, including the password, security settings, and even the email address associated with it. Assuming that two-factor verification (discussed later in this lesson) has not been enabled for this Apple ID, you can sign in with only the email and password to manage most settings. To edit password and security settings of an Apple ID, you must also answer two of the three security questions that were set during the ID creation.
As a convenience to the user, multiple email addresses can be associated with an Apple ID as long as those addresses aren’t associated with another Apple ID. Again, any additional email address must be verified by opening a web link embedded in an automated email sent to the new email address.
With the exception of Apple IDs that use Apple domains (mac.com, me.com, or icloud.com), any email associated with an Apple ID can also be changed as long as the email address is verified, including the primary address used to create the Apple ID. This process is obviously convenient for a user who wishes to change an Apple ID, but it also creates a problem for any administrator who tries to use shared Apple IDs for management tasks.
For example, a school administrator could set up a single Apple ID for use by all the teachers who share school-owned iPads. Any teacher who wants to install additional apps would need to know the Apple ID username and password. However, by default, anyone with access to that Apple ID could sign in to https://applied.apple.com and change the primary email to another email unbeknownst to the other individuals using that Apple ID. Doing so would prevent all others from accessing the Apple ID and its associated services. Fortunately, this problem can be avoided by setting up two-step verification for shared Apple IDs.
Apple ID Two-Step Verification
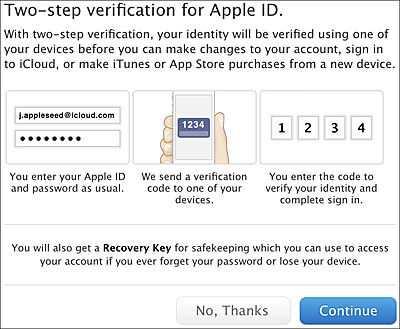
To enhance the security of any Apple ID, including the ability to prevent other users from modifying shared Apple IDs, you can configure two-step verification. As you’ve learned, most aspects of an Apple ID can be modified by anyone who knows the email and password. The only additional verification is the three security questions set during the creation of the Apple ID. Unfortunately, this form of verification is known to be easily circumvented using social hacking techniques.
Setting up two-step verification disables the security questions in favor of more robust verification methods. Currently, to enable two-step verification for an Apple ID, you must use the password and security settings at the Apple ID management website (https://applied.apple.com). The process involves adding an Apple device or SMS-capable mobile phone as a verified “trusted” device.
After a device is indentified as a trusted device, it’s used for the second step (password creation being the first step) of authenticating an Apple ID. If a user attempts to sign in to an Apple ID service that requires two-step verification, a random security code will be sent to the trusted device. The random code received by the trusted device must be entered to the authenticated service for access to be granted. At the time of this writing, only a few Apple websites require two-step verification, including the Apple ID management site and the Apple Deployment Programs site.
Enabling two-step verification also generates a complex Recovery Key that may be used in lieu of the old security questions should the trusted device be lost or unable to receive the random verification codes. In other words, the Recovery Key is a “backup second step.” Apple does not provide a method for securely storing your Apple ID Recovery Key. That is left up to you.
Maintaining the trusted devices and Recovery Key is very important. Once two-step verification is enabled, you must always provide two steps of verification to access an Apple ID. If you cannot provide at least two of the three verification methods (random code via trusted device, Recovery Key, and password), the Apple ID will not be accessible, even with Apple’s help. Assuming you can successfully sign in to the Apple ID management website, both the trusted devices and Recovery Key can be modified from the password and security settings.
Shared Apple IDs
When considering how Apple ID fits into your deployment plans, think of two general categories of Apple ID: those used solely by individuals and those shared by individuals on the behalf of an organization.
Technically, every Apple ID should be accessed by only a single user. In fact, the Apple Support FAQ for Apple ID states in very plain language that, “You shouldn’t share your Apple ID account information with other people. Each person should have their own Apple ID.” Clearly, Apple expects every user in your organization to have a unique Apple ID. Historically, this precedent has been a source of contention for organizations trying to manage groups of Apple devices.
One issue arises in primary education because Apple IDs can be created only for individuals age 13 and older, which means younger students can’t secure a valid Apple ID.
Further, the prospect of having to create hundreds or even thousands of individual Apple IDs may seem too daunting for administrators to manage. These issues can be resolved for educational institutions with the Apple ID for Students program covered later in this lesson.
The other primary reason organizations have resorted to sharing Apple IDs is to work around the App Store authorization mechanism. In short, any item acquired from the App Store (including free items) must be authenticated with an Apple ID. This presents a significant licensing issue for some organizations because assets purchased by the organization cannot be transferred to individuals. This issue can be resolved by using managed licenses as part of the Apple Volume Purchase Program covered later in this lesson.
In other cases, administrators may simply not understand how to properly deploy assets to individual users and are using shared Apple IDs because they haven’t learned best practices. Hopefully, guides like this one will help alleviate this practice, because using shared Apple IDs is often not the best method for managing iOS and OS X devices.
Institutional Apple IDs
In some specific cases it may be desirable for an organization to create Apple IDs that are shared amongst administrators. This is true for any important organizational resource managed by individuals; a backup individual should always be in place. In these cases, the resources accessed by an Apple ID may be very difficult to recover should the primary responsible individual be unable to access the resource.
The simplest method for sharing an Apple ID is to securely communicate the Apple ID and password to another responsible individual in the organization. The other responsible individuals should also have knowledge of any additional security information associated with the Apple ID, such as information about the two-step verification process. Another best practice is to associate a group email address or multiple email addresses with a shared institutional Apple ID.
The following is a list of example services with which an institutionally shared Apple ID may be best for your organization:
- Apple ID used for Apple Configurator systems
- Apple Push Network service certificate creation
- Apple Deployment Programs facilitators
- Enterprise Developer facilitators
- GSX Program facilitators