- Reference 2.1 Understanding Apple’s Goals
- Reference 2.2 Device Management and Supervision
- Reference 2.3 Apple ID Considerations
- Reference 2.4 iCloud in Managed Environments
- Reference 2.5 Apple Deployment Programs
- Reference 2.6 Deployment Scenarios
- Exercise 2.1 Configure Your Client Mac
- Exercise 2.2 Create Apple IDs
- Exercise 2.3 Verify Administrator Apple ID Access
- Exercise 2.4 Configure Your iOS Device
Reference 2.4 iCloud in Managed Environments
For your users, iCloud may very well become the single most important service accessed by your Apple deployment. After all, it’s the personal documents and settings that are most important to each user. If you don’t have a plan for some form of off-device user document storage, at best you’re doing your users a disservice by not providing an easy method for sharing content. At worst, if you’re not providing some form of backup, you’re potentially setting up your users for tragic failure should a device be lost or become irreparably damaged.
Many third-party storage solutions have excellent implementations for iOS and OS X; and there are many great backup solutions for OS X. However, because of the security design in iOS, iCloud is the only solution that provides both cloud-based document sharing and cloud-based system backup.
It’s unfortunate that many organizations prevent iCloud use due to a lack of understanding of how to properly manage iCloud services. This section explores some best practices for setting up iCloud in managed environments.
iCloud Setup
Strictly speaking, iCloud services aren’t free, They are included as part of the purchase of an Apple device. Any Apple ID can gain free iCloud services by signing in on an iOS or OS X device within the Setup Assistant or via iCloud settings. Users can sign in with an existing Apple ID and it will be “upgraded” to include iCloud services, or they can create a new Apple ID with iCloud services.
An important caveat is that a single Apple device can add iCloud services to only a specific number of Apple IDs. Every time an Apple ID is upgraded or created during iCloud setup, the specific Apple device is verified by Apple’s iCloud service. At the time of this writing, an Apple device can add iCloud services to an Apple ID three times during the device’s lifespan. That is, a single Apple device can add iCloud services for three Apple IDs. If you attempt to add iCloud services to a fourth Apple ID on the device, the system will report an error.
This iCloud setup limitation should be considered when planning your deployment. If you are planning to give each user her own Apple device, it’s recommended that each user set up her iCloud service when first receiving the device. The best practice is to have the user sign in while using the Setup Assistant. This will set up iCloud services, and also configure the user’s Apple ID for other Apple services on the device including the App Store, iTunes, iMessage, and Face Time.
On the other hand, if you are planning to deploy and share Apple devices among multiple users, you need to carefully consider how to add iCloud services. Depending on the number of individual Apple IDs you require, it may not be possible to give all your users iCloud access using standard methods.
iCloud Content and Backup
A key feature of iCloud is the ability to save user documents to Apple’s servers and automatically push those documents to other Apple devices. Documents saved in iCloud are also available by going to http://www.icloud.com using any modern web browser. For iOS devices, iCloud also offers the ability to back up app and system configuration.
At the time of this writing, the basic iCloud service includes 5 GB of storage. Many users may easily fill this storage allotment, especially when using iCloud for data backup. Apple makes more iCloud storage available for a yearly subscription price. iCloud storage settings, including the ability to purchase more storage, can be managed from the iCloud settings on an iOS or OS X device.
If you are going to rely on iCloud for your users’ storage needs, your deployment plans must include methods for dealing with storage limitations. If the budget is available, you can plan for the annual purchase of more storage. Regardless of the amount of storage, though, you should always budget some time to train your users on how to manage storage using the iCloud settings.
iCloud Security
Your organization may have legitimate security concerns that information could leak though iCloud services. This concern is valid for any sharing service, including legacy services that have been in use for years such as simple email. When security is a concern for your organization, your deployment plans must address that concern.
To start, the iCloud service itself employs an array of security technologies. All iCloud data is encrypted in transit, and nearly all data stored in iCloud remains encrypted on Apple’s servers. Only the iCloud mail service (hosted on mac.com, me.com, or icloud.com domains) stores email messages in an unencrypted format on the server, but this is a standard practice that permits interoperation with other email services. In this case, a common practice is to use optional S/MIME encryption to protect email messages.
As an administrator, you have additional management options for controlling iCloud access on iOS devices. Using a profile, you can restrict the ability to save documents or backups to iCloud. For more specific control, an administrator can also manage the ability of individual apps to share documents with other apps and services. Doing so limits an app’s ability to interact with iCloud or any other document-sharing service.
In addition to these management features, Apple has engineered iOS to always enforce strict segregation between services. For example, email hosted by your organization is stored in its own encrypted container on iOS, separate from other email services. In this case, iCloud services are also stored separately from other services. This security architecture allows your organizational services to live alongside personal services such as iCloud.
Given the advanced security architecture built into iOS and an administrator’s ability to further control what is shared through iCloud, you may consider the advantages of allowing iCloud for personal use. By encouraging your users to take advantage of iCloud for personal use, they will keep their personal information away from your organizational services. Consider this a win-win for both sides as users can use an organizational device for occasional personal communications and administrators can keep those personal communications off their services.
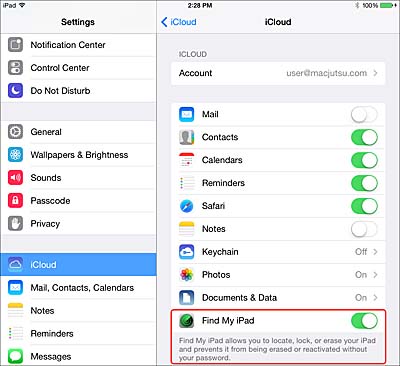
Find My Device and Activation Lock
One of the most useful features of iCloud is the Find My Device service, which allows you to remotely locate a lost iOS or OS X device. This service uses the device’s built-in wireless capabilities to pinpoint the misplaced or stolen device. The location of an iOS device with built-in GPS capabilities are accurate to within one meter, while all other devices are accurate within the range of a Wi-Fi network.
The first time an Apple ID is signed in to iCloud on a device, the system will prompt the user to enable the Find My Device service. This service can also be enabled or modified in the iCloud settings.
Lost devices can be located by signing in to the Find My iPhone app for iOS, or using any modern web browser to sign in to http://www.icloud.com and then selecting Find My iPhone. They will allow you to locate any lost iOS or OS X device that has Find My Device enabled. Within this interface, you can also remotely force the device to make a sound, to lock and display a message, or completely wipe the system contents.
Normally, enabling Find My Device will also enable another security feature known as Activation Lock. Should a lost device with Activation Lock enabled be wiped and reset, the subsequent Setup Assistant process will not proceed unless a user enters the password associated with the Apple ID that originally enabled Find My Device. Activation Lock is a theft-deterrent measure that prevents another user from completing the Setup Assistant without knowing the previously used Apple ID.
A single Apple ID can enable Find My Device and Activation Lock for multiple devices, but only one Apple ID per device is allowed for these services. iOS devices don’t allow you to add additional Apple IDs for Find My Device and Activation Lock. On OS X, attempting to sign in with another Apple ID for these services will require that the user authenticate using the password for the previously enabled Apple ID. These implementations effectively prevent someone from surreptitiously changing the Apple ID used for Find My Device and Activation Lock.
However, the fact that only one Apple ID can be used for Find My Device and Activation Lock presents a problem for some organizational-owned devices. Specifically, your deployment plan needs to consider which Apple ID will be used to enable these security features. In some organizations, sharing an Apple ID among trusted administrators may be best. In other situations, individuals may be required to use their own Apple IDs and then work with an organization’s administrators if they need to use Find My Device.