OS X Server Essentials 10.10: Introducing Account Management
Reference 11.1 Introducing Account Management
OS X Lion introduced the concept of profiles that contain configurations and settings, and OS X Yosemite expands on the idea. By assigning profiles to users, user groups, devices, or groups of devices, you can more effectively control them.
With profiles, you can achieve a range of results including but not limited to the following:
- Controlling settings on mobile devices and computers
- Restricting resources to specific groups or individuals
- Securing device use in key areas such as offices, classrooms, or open labs
- Customizing the user experience
- Providing apps and books to the users
Levels of Management
You can create settings for four types of accounts:
- User—This usually relates to a specific person. This is the account that the person identifies herself with when logging in to the computer. A user’s short name or user ID (UID) number uniquely identifies the user on a system.
- Group—This represents a group of users, a group of groups, or a mixture of both.
- Device—Similar to a user account, this is the singular entity that represents a given piece of hardware. This can be either a computer or an iOS device. Device accounts are uniquely identified by their Ethernet ID (MAC address), serial number, international mobile equipment identity (IMEI), or mobile equipment identifier (MEID).
- Device group—This represents a grouping of computers or iOS devices or both. A device group can include other device groups nested in it or a mixture of both individuals and nested groups.
Not all management levels make sense for all purposes, so when setting policy, you have to decide what is appropriate. For example, you might want to define printers by device group because a typical situation has a group of computers located geographically close to a specific printer. You may want to set virtual private network (VPN) access via a group of users such as remote salespeople. And individuals might have specific application access rights granted to them.
Each level can have a default group of settings and then custom settings. Mixing and layering profiles with conflicting settings is not recommended. The results may not be what you expected.
If a user or user group has an assigned profile and the user logs in to the user portal website to enroll an OS X computer, the profiles assigned to that user will be applied to that computer regardless of who logs in to that computer. The same applies if they have an iOS device assigned to them as a user.
Managing Preferences for Users in a Group
Although you can set up preferences individually for users with network accounts, it’s more efficient to manage preferences for the groups to which they belong. Like with individual users, group management is applied if the user enrolling the device is a member of a group that has management set for it. Groups can also be used for applying Volume Purchase Program (VPP) enrollment to a wide swath of users rather than inviting users individually.
Managing Device Group Accounts
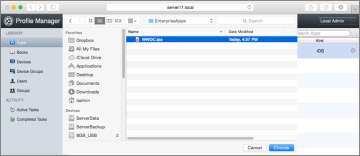
A device group account is set up for a group of OS X computers or iOS devices that have the same preference settings and are available to the same set of users and groups. You create and modify these device groups in Profile Manager.
When you set up a device group, make sure you have already determined how the devices are identified. Use descriptions that are logical and easy to remember (for instance, the description might be the computer name). This also makes it easier to find the devices to add them to the correct device group.
You can import lists of devices into Profile Manager via a comma-separated value (CSV) file The file needs to be structured like this:
name, serial number, UDID, IMEI, MEID
Leave a field empty if you’re not using that value.
Managing Apps
Apps—both Enterprise and those purchased via VPP—can be assigned to users and groups. Only Enterprise apps can be assigned to devices and device groups. Enterprise apps are ones that are developed “in-house” by a company, typically for internal needs, and are not distributed via the App Store.
Apps purchased through VPP automatically show up in the Apps pane in Profile Manager. Enterprise apps need to be uploaded into Profile Manager.
The VPP apps will be assigned to the devices at the next push, but in-house Enterprise apps get automatically pushed.
Delivering Profiles
Once created, profiles can be delivered in a number of ways:
- Via the user portal website—Users log in to the portal with their account credentials and are presented with the profiles assigned to them.
- Via an email to the user—The profile is a simple text file formatted in Extensible Markup Language (XML), so it is easily transported.
- Web link—The profile can be published on a website for users to visit and download.
- Automatic push—The profile gets automatically pushed to the device with no user interaction (the device must be enrolled for this to work).
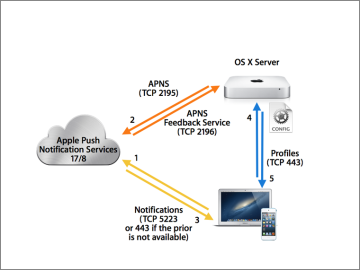
Automatic push relies on the Apple Push Notification service (APNs). This service is hosted by Apple and is provided to allow secure push notification to client devices. Once a server is configured to utilize APNs, client devices enrolled for management in Profile Manager check in with APNs and wait for notification signals to be sent by the Profile Manager via APNs. No data is included in the notification beyond informing the client that Profile Manager has something for it. This keeps data secure between Profile Manager and the client.
Here is the push notification process:
- An enrolled device makes contact with APNs and keeps a lightweight communication going between them. This happens any time the enrolled device has a network chance, as would occur when being turned on, changing networks, or switching network interfaces.
- The Profile Manager service contacts APNs when it needs to notify an enrolled device or group of devices of a new or changed profile. APNs has the ability to send feedback to the Profile Manager service.
- APNs notifies the device to get in touch with the associated Profile Manager service in which it is enrolled.
- The device communicates with the Profile Manager service once notified.
- The Profile Manager service sends the profile to the device.
A list of installed profiles is available in OS X in Profile preferences. An equivalent list is available in iOS when you tap Settings > General > Profiles.
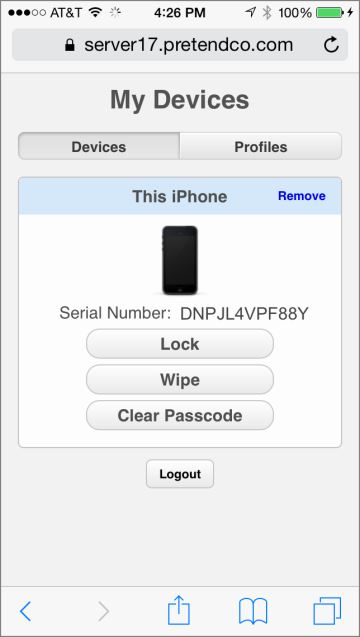
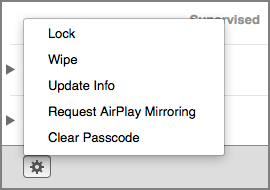
Remotely Locking or Wiping a Device
Once enrolled, a device or group of devices can be remotely locked or wiped. In this example, a remote lock will be performed. A remote wipe can be attempted, but do it only on a device you don’t mind reconfiguring. Administrators can lock the device via Profile Manager, and users can lock it via the user portal website.
Upon requesting a lock, a confirmation pane will appear, a passcode will be requested, and the lock command will be sent. Mac computers are shut down, and an Extensible Firmware Interface (EFI) passcode is set, so it needs to be entered to use the computer again. For iOS devices, the screen is locked, and the passcode is enforced.
There are two ways devices can be locked or wiped:
Profile Manager—Log in to the Profile Manager web app, and select the device or group of devices to be locked. In the Action (gear icon) pop-up menu, choose Lock. The content of the Action menu will vary depending on whether it is a device or device group.
User portal—Once users log in, each device they enrolled will be displayed in the Devices pane. The lock and wipe choices are presented in each device listed.
Which Preferences Can Be Managed?
In addition to various other settings for user, group, device, and device group accounts, Profile Manager provides control over the preferences in Table 11-1. Table 11-2 describes the manageable preferences payloads for devices and device groups.
Table 11.1 Manageable Preferences Payloads for Users and Groups
Preference |
OS X |
iOS |
Description |
General |
✓ |
✓ |
Profile distribution type, how the profile can be removed, organization, and description |
Passcode |
✓ |
✓ |
Define passcode requirements such as length, complexity, reuse, and so on |
✓ |
✓ |
Configure email settings such as servers, account name, and so on |
|
Exchange |
✓ |
✓ |
Configure Exchange ActiveSync settings |
LDAP |
✓ |
✓ |
Configure connection to LDAP server |
Contacts |
✓ |
✓ |
Configure access to CardDAV server |
Calendar |
✓ |
✓ |
Configure access to CalDAV server |
Network |
✓ |
✓ |
Configure network setting on the device, including wireless and wired |
VPN |
✓ |
✓ |
Configure VPN settings: L2TP, PPTP, IPSec (Cisco), CiscoAnyConnect, Juniper SSL, F5 SSL, SonicWALL Mobile Connect, and Aruba VIA |
Certificate |
✓ |
✓ |
Allow the installation of PKCS1 and PKCS12 certificates |
SCEP |
✓ |
✓ |
Define connection to Simple Certificate Enrollment Protocol (SCEP) server |
Web Clips |
✓ |
✓ |
Display defined Web Clips as application icons |
Fonts |
✓ |
✓ |
Distribute fonts |
Airplay |
✓ |
✓ |
Define which AirPlay devices can be used |
Global HTTP Proxy |
✓ |
Define a proxy to be used by the device |
|
Airprint |
✓ |
Define settings for the device to connect to AirPrint printers |
|
Content Filter |
✓ |
Define which URLs can be reached by the device |
|
Domains |
✓ |
Define email domains that won’t be marked in Mail and web domains from which documents will be considered managed |
|
Security and Privacy |
✓ |
✓ |
Control if diagnostic and usage data gets sent to Apple; define password and lock restrictions, plus whether user can override Gatekeeper (OS X only) |
Identification |
✓ |
Configure identification information of user |
|
Restrictions |
✓ |
✓ |
Define application and content restrictions (separate OS X and iOS versions) |
Subscribed Calendars |
✓ |
Configure calendar subscriptions |
|
APN |
✓ |
Configure carrier settings such as the access point name (advanced use only) |
|
Messages |
✓ |
Configure connection to Jabber or AIM chat servers |
|
AD Certificate |
✓ |
Specify the settings for retrieving a certificate for your computer from Active Directory |
|
Login Items |
✓ |
Specify applications, items, and network mounts to launch at login |
|
Mobility |
✓ |
Define mobility settings for OS X clients to allow cached credentials and portable home directories |
|
Dock |
✓ |
Configure Dock behavior |
|
Finder |
✓ |
Configure Finder settings |
|
Printing |
✓ |
Configure printing settings and access to printers or print queues |
|
Parental Controls |
✓ |
Define settings for Parental Controls such as content filtering and time limits |
|
Accessibility |
✓ |
Manage Accessibility settings |
|
Single Sign-On |
✓ |
Configure Kerberos settings |
|
Custom Settings |
✓ |
Apply custom preferences for items not defined in other payloads; similar to applying preference manifests in WGM |
Table 11.2 Manageable Preferences Payloads for Devices and Device Groups
Preference |
OS X |
iOS |
Description |
General |
✓ |
✓ |
Profile distribution type, how the profile can be removed, organization, and description |
Passcode |
✓ |
✓ |
Define passcode requirements such as length, complexity, reuse, and so on |
Fonts |
✓ |
✓ |
Distribute fonts |
Single App Mode |
✓ |
Define an app that will be the only one the device will open |
|
Global HTTP Proxy |
✓ |
Define a proxy to be used by the device |
|
Airprint |
✓ |
Define settings for the device to connect to AirPrint printers |
|
Content Filter |
✓ |
Define which URLs can be reached by the device |
|
Domains |
✓ |
Define email domains that won’t be marked in Mail and web domains from which documents will be considered managed |
|
Airplay |
✓ |
✓ |
Define which AirPlay devices can be used |
✓ |
Configure email settings such as servers, account name, and so on |
||
Exchange |
✓ |
Configure Exchange ActiveSync settings |
|
LDAP |
✓ |
Configure connection to LDAP server |
|
Contacts |
✓ |
Configure access to CardDAV server |
|
Calendar |
✓ |
Configure access to CalDAV server |
|
Network |
✓ |
✓ |
Configure network setting on the device, including wireless and wired |
VPN |
✓ |
✓ |
Configure VPN settings: L2TP, PPTP, IPSec (Cisco), CiscoAnyConnect, Juniper SSL, F5 SSL, SonicWALL Mobile Connect, and Aruba VIA |
Certificate |
✓ |
✓ |
Allow the installation of PKCS1 and PKCS12 certificates |
AirPlay |
✓ |
✓ |
Define AirPlay destination settings |
SCEP |
✓ |
✓ |
Define connection to Simple Certificate Enrollment Protocol (SCEP) server |
Web Clips |
✓ |
Display defined Web Clips as application icons |
|
Identification |
✓ |
Configure identification information of user |
|
AD Certificate |
✓ |
Specify AD certificate settings |
|
Directory |
✓ |
Specify OD server settings |
|
Restrictions |
✓ |
✓ |
Define application and content restrictions (separate OS X and iOS versions) |
Subscribed Calendars |
✓ |
Configure calendar subscriptions |
|
APN |
✓ |
Configure carrier settings such as the access point name (advanced use only) |
|
Login Items |
✓ |
Specify applications, items, and network mounts to launch at login |
|
Mobility |
✓ |
Define mobility settings for OS X clients to allow cached credentials and portable home directories |
|
Dock |
✓ |
Configure Dock behavior |
|
Printing |
✓ |
Configure printing settings and access to printers or print queues |
|
Parental Controls |
✓ |
Define settings for parental controls such as content filtering and time limits |
|
Security and Privacy |
✓ |
✓ |
Control if diagnostic and usage data gets sent to Apple; define password and lock restrictions, FileVault, plus whether user can override Gatekeeper (OS X only) |
Custom Settings |
✓ |
Apply custom preferences for items not defined in other payloads (similar to applying preference manifests in WGM) |
|
Directory |
✓ |
Configure binding to directory services |
|
Time Machine |
✓ |
Configure Time Machine preferences |
|
Single Sign-On |
✓ |
Configure Kerberos settings |
|
Login Window |
✓ |
Configure login window options, such as messages, appearance, access, and Login/LogoutHooks |
|
Finder |
✓ |
Configure Finder settings |
|
Software Update |
✓ |
Define an Apple Software Update server to be used by the computer |
|
Accessibility |
✓ |
Manage Accessibility settings |
|
Energy Saver |
✓ |
Define Energy Saver policy such as sleeping, timed actions, and wake settings |
|
Xsan |
✓ |
Define Xsan membership |
|
Custom Settings |
✓ |
Apply custom preferences for items not defined in other payloads; similar to applying preference manifests in WGM |
Layering and Multiple Profiles Considerations
In previous versions of OS X management, you could create different behaviors by layering management techniques reflecting users, groups of users, devices, and groups of devices. Although Profile Manager also shows those same four management levels, you need to be careful when building profiles.
The general rule is to avoid layering profiles that manage the same preferences, but this is not a strict rule. Some profiles can be additive, and others can collide, so you need to be aware of which are which.
Multiple profiles that contain different settings for the same preferences result in undefined results. There is no order of preference applied to the multiple profiles, so you will not have a predictable outcome.
Payloads that should remain exclusive include the following:
- AD Certificate
- APN
- Directory
- General
- Global HTTP Proxy
- Identification
- Restrictions
- Security & Privacy
- Single App Mode
- Single Sign-On
- Xsan
Payloads that can be combined include the following:
- Accessibility
- AirPlay
- AirPrint
- Calendar
- Certificate
- Contacts
- Content Filter
- Custom Settings
- Dock
- Domains
- Energy Saver
- Finder
- Fonts
- Exchange
- LDAP
- Login items
- LoginWindow
- Messages
- Mobility
- Network
- Passcode
- Parental Controls
- Printing
- SCEP
- Software Update
- Subscribed Calendars
- Time Machine
- VPN
- Web Clips