- Reference 4.1 OS X Server Benefits
- Reference 4.2 OS X Server Setup
- Reference 4.3 TLS/SSL Certificates
- Exercise 4.1 Prepare Your Mac for OS X Server for Yosemite
- Exercise 4.2 Install OS X Server for Yosemite
- Exercise 4.3 Configure OS X Server for Yosemite
- Exercise 4.4 Configure Server on Your Client Computer (Optional)
Reference 4.3 TLS/SSL Certificates
Transport Layer Security (TLS) and its predecessor, SSL, are protocols for the secure transmission of data between hosts. More specifically, TLS/SSL technology is used to prove your server’s identity to client devices and to encrypt communication between your server and client devices. This encryption isn’t just recommended to secure OS X Server services; it’s required for any MDM service including Profile Manager. This section starts with the basics of TLS/SSL certificates and then provides recommendations for certificate best practices in regard to managing Apple devices.
Understanding Certificates
To enable TLS/SSL communications, you must configure your server with a TLS/SSL certificate (also referred to as simply a certificate). A certificate is a file that identifies the certificate holder. A certificate specifies the permitted use of the certificate and has an expiration date. This is why certificates must be renewed on a regular basis (most often annually).
Importantly, a TLS/SSL certificate also includes a public key infrastructure (PKI) public key. This public key is mathematically tied to a private key that is securely stored on the server. Data encrypted with one key can be decrypted only by using the other key. Thus, if you can decrypt data with one key, it proves that the data was encrypted with the other key.
To initiate secure TLS/SSL connections, client devices download the certificate (containing the public key) from your server. If a client can successfully verify the identity of the server from the certificate, it will use the public key to begin secure communications with the server. This raises the question, how exactly does a client device verify, or trust, a certificate?
The answer is that a certificate is verified by its digital signature. A certificate is either self-signed or signed by a certification authority (also known as a certificate authority or, more simply, a CA). A self-signed certificate, as the name implies, doesn’t require the involvement of other CAs; thus, OS X Server will automatically create a self-signed certificate during the setup process. You can use a self-signed certificate for most TLS/SSL services, but self-signed certificates created by OS X Server (and most other servers) are not trusted by Apple devices for MDM services.
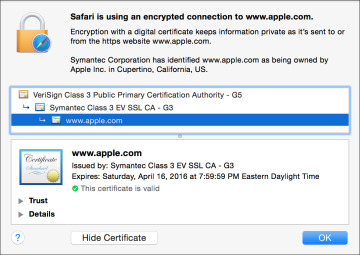
In other words, if you need to manage Apple devices, you will need to configure a certificate that has been signed by a verifiable CA. Certificates used by servers are most often signed by an intermediate CA, which is a CA whose certificate is signed by another CA. The PKI infrastructure allows for a hierarchical chain of certificates, commonly known as a chain of trust. For example, the following figure shows the chain of trust for https://www.apple.com, which can be revealed in Safari by clicking the lock to the left of a web address:
The certificate for www.apple.com is signed by an intermediate CA with the name of Symantec Class 3 EV SSL CA – G3, and that intermediate CA is signed by a CA with the name of VeriSign Class 3 Public Primary Certification Authority – G5. You can follow a chain of certificates, starting with a signed certificate, following it up to the intermediate CA, and ending at the top of the chain. The certificate chain ends with a CA that signs its own certificate, which is called a root CA. This raises the question, how does a device know whether it can trust a CA?
The answer is that trust has to start somewhere. iOS and OS X include a collection of root and intermediate CAs that Apple has determined are worthy of trust out of the box. By extension, your Apple devices also trust any certificate or intermediate CA whose certificate chain ends with one of these CAs.
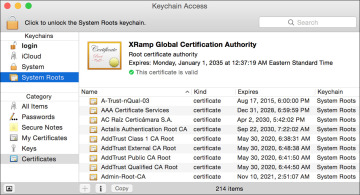
Although you can’t directly inspect the list of root certificates included on iOS devices, you can on an OS X computer from the Keychain Access application. Open Keychain Access (in the Utilities folder). In the upper-left Keychains column, select System Roots. Note that in the following figure the bottom of the window states that there are more than 200 trusted CAs or intermediate CAs by default in Yosemite:
Certificate Signed by an Open Directory CA
Again, any MDM service must use a TLS/SSL certificate signed by a trusted CA. This limits you to one of two choices if using Profile Manager as your MDM service: a certificate signed by a widely trusted CA (as covered in the next section) or a certificate signed by your own local Open Directory CA. Fortunately, OS X Server makes this latter choice an easy option by automatically creating an Open Directory CA and signing your server’s TLS/SSL certificate during the creation of an Open Directory master.
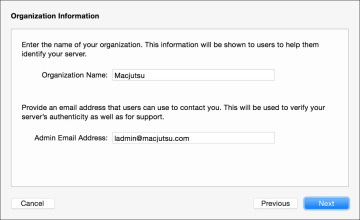
When creating an Open Directory master from the Server app, Setup Assistant will guide you through several screens. One of the setup screens allows you to enter organizational information. This information will be used to create an Open Directory CA that will then be used to sign an intermediate CA, which is then used to sign your server’s TLS/SSL certificate. This process will also create a code signing certificate that will come in handy for verifying profiles, as covered in Lesson 6, “Configuration and Profiles.”
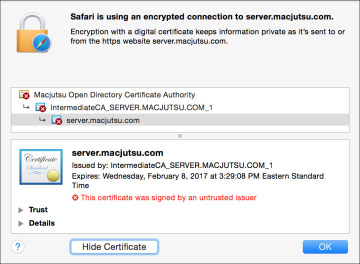
Assuming you completed the Open Directory master creation before acquiring other certificates, the Server app will automatically configure all supported services to use the certificate signed by the Open Directory CA. You can verify this by simply navigating to your server’s default secure website, https://hostname, where “hostname” is the name of your server. Even if the Websites service on your server isn’t turned on, you will still see a default web services page and can inspect the certificate used to protect the site.
You’ll note that even though a chain of trust has been created, you still have the fundamental problem that Apple devices, by default, do not trust your server’s Open Directory CA. In a managed environment, this problem can be easily resolved by using a trust profile, also covered in Lesson 6, “Configuration and Profiles.”
In fact, deploying a trust profile is required for the enrollment of most MDM services, including Profile Manager. Thus, if you or your staff is going to be directly responsible for managing the enrollment of Apple devices, using a certificate signed by the Open Directory CA is a perfectly acceptable solution for most deployments.
Issues with an Untrusted Certificate
In some environments, using a certificate signed by an Open Directory CA is not the recommended solution. For example, your organization may require that all TLS/SSL services use certificates that meet a certain specification or are provided by a specific vendor.
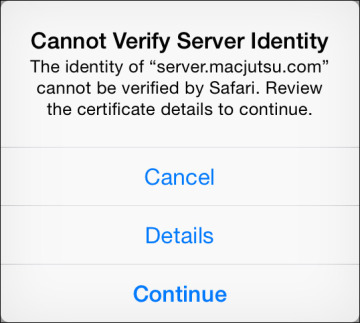
Alternately, if your environment relies upon users self-enrolling their own devices, you don’t want the first user experience of your management solution to be a warning message. The following warning message appears on an unmanaged iOS device when connecting for the first time to an MDM service using a certificate signed by an untrusted Open Directory CA:
Not only does this type of warning message make your management solution look sketchy, it means that you (and your users) can’t trust any connection made to your management server. In other words, when connecting from an unmanaged device, you will have no way of identifying a legitimate connection to your server from an illegitimate server acting as your server or a server that is attempting a man-in-the-middle attack.
Further, you don’t want to establish that it’s OK for your users to click Continue when presented with this warning. Quite to the contrary, you should be instructing them that accepting connections to unverified servers is extremely dangerous.
Certificate Signed by a Widely Trusted CA
If you determine that your server needs a certificate signed by a widely trusted CA, the Certificates pane of the Server app provides two main methods for configuration: getting a trusted certificate by generating a certificate signing request (CSR) or importing an existing certificate identity.
Get a Trusted Certificate
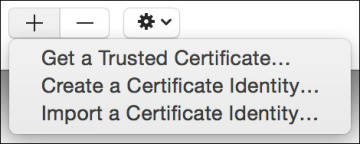
The default behavior for the Add (+) button at the bottom of the Certificates pane in the Server app is to open an assistant that will step you through the process of getting a trusted certificate. Alternately, if the Certificates pane is set to show all certificates (via the Action menu), then the Add (+) button reveals a pop-up menu.
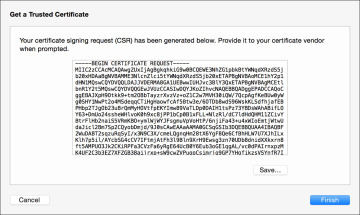
The Get a Trusted Certificate assistant will create a new certificate identity consisting of an unsigned certificate and a private/public key pair. After you enter contact information for the certificate, the system will present a CSR. You will need to copy and paste (or save to a text file) the CSR content. The act of providing a CSR to a CA vendor is the most common method for acquiring a certificate signed by a widely trusted CA.
At this point, you will need to identify a CA vendor. Your organization may already work with a CA vendor, so that will likely be your first choice. Otherwise, the only recommendation is choosing a CA vendor that works with Apple devices. When selecting a CA vendor, an obvious quick test is that an Apple device can establish a secure connection to the vendor’s website.
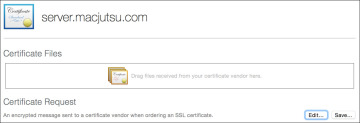
After acquiring a TLS/SSL certificate subscription from a CA vendor, you will need to give the vendor your server’s CSR. Most CA vendors will accept the CSR content via a simple paste into a website. After the CA vendor has validated and signed your certificate, they will return it to you as a download. The download will often include the CA vendor’s intermediate and root certificates. Double-click the pending certificate in the Server app and drag all certificates provided by the CA vendor into the appropriate area.
Import a Certificate Identity
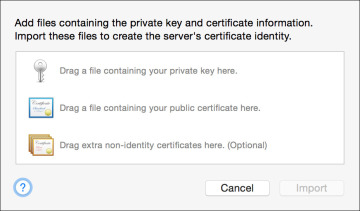
Again, if the Certificates pane is set to show all certificates (via the Action menu), then the Add (+) button reveals a pop-up menu. From this menu, you can select the option to import a certificate identity. This option assumes you already have a valid certificate identity consisting of a signed certificate and a private/public key pair. This is often the case if your organization uses a centralized certificate repository or if your organization has a wildcard certificate that can be used for multiple services. The term wildcard refers to the fact that the certificate can be used with any host name inside a specific domain.
If this is the case, someone else has already done all the hard work for you and will provide you with the appropriate certificates and private/public key pair. Transporting a private key in the clear is dangerous, so the key is often stored in an encrypted document. Further, to make certificate identities easier to transport, this encrypted document will also contain all the appropriate certificates. The most common file types are .pfx and .p12, both of which share a similar encrypted format.
The person providing you with the certificate identity will also have to provide you with the encryption key used to protect the document containing the private key. Once you have all the certificate identity documents, simply drag them to the certificate import window in the Server app and then provide the encryption key.